What caused the United Kingdom to drop the crown once more?
A National Perception of Value
One nation’s trash is another nation’s treasure
Drawing American Factories
Come to America and be a Happy Factory
The Invisible Hand of AI Disinformation
An intro to how AI can trick you
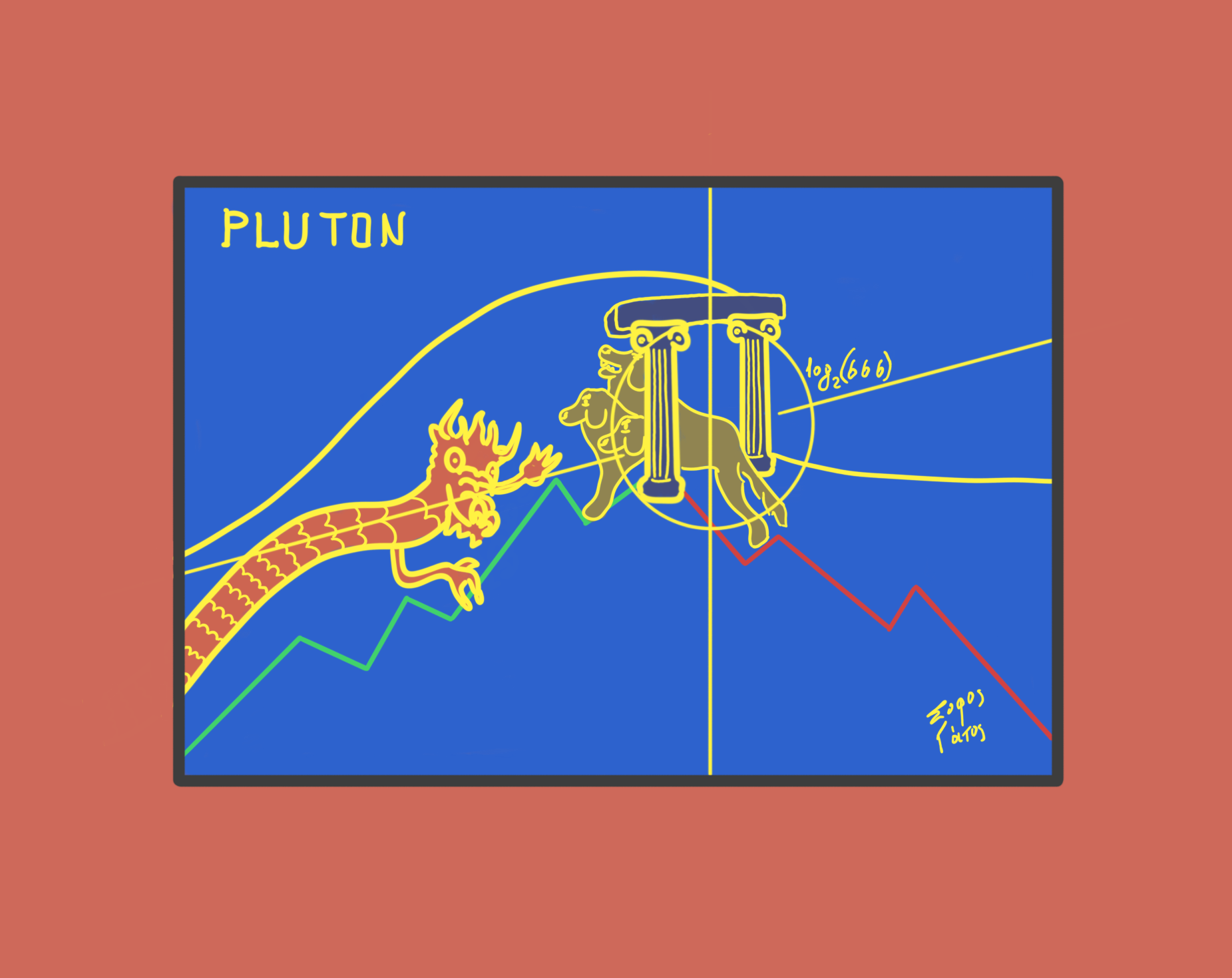
Is there a looming global crisis? How the internal disorder of the US sets the world on the brink of depression
Guaranteed by Mr. Maverick
The Blueprint for International Relations (or how to read the World)
If you only have ten minutes to understand what is happening globally, read this.